Your personal health data is not only very private, but it is very valuable. Healthcare organizations across North America (and the world) are continually needing to invest in security programs that protect their patient information through physical security, technology, and managing human-led processes and workflows.
When is the last time your security program had a check-up?

Onliner Adam Kehler is a Principal Consultant and Healthcare Practice Lead with our Risk Security and Privacy practice, and a passionate believer in the importance of mature security practices for healthcare organizations. Over the last number of years, Adam has been asked to speak at numerous conferences and events on the importance of effective security measures being implemented in the healthcare industry.
Recently he co-authored ‘Health Center Security & Compliance System Implementation Guide’, aimed at helping health center IT leaders when they are implementing a new security system. The piece was then published by HITEQ Center, which is a federal resource center for Community Health Centers in the U.S., providing resources to help them adopt technology and comply with federal requirements and incentive programs. We are so pleased to be able to share a copy of the guide with you, as well as some of Adam’s high-level thoughts on the topic.
When asked why the guide is important, Adam replied “Even though compliance with the standards of HIPAA Security Rule has been required for 14 years, the specifics on how to comply are still widely misunderstood in the industry. Security Risk Analysis is not a checklist, description of security controls, or vulnerability scan. It is a ‘thorough and accurate’ assessment of risks to the confidentiality, integrity and availability of patient information.”
In the Guide, Adam shares that many healthcare organizations mistakenly think that HIPAA is about completing a checklist instead of what it is intended to be – a security risk management program. This misconception leads to serious gaps in security system implementations. For something as valuable as patients’ personal health information, it’s critical to make sure it’s done right the first time and continually managed as part of an ongoing program.
Implementation of a proper security risk management program for any healthcare organization has numerous complexities that cannot be skipped or misunderstood. While breaches can occur for any organization, when steps are missed and methodologies not followed carefully, the associated risks increase tenfold.
All it takes is a quick look at the numbers, specifically the number of resolution agreements and settlements that have been handed out by the HHS Office for Civil Rights (OCR), for lack of compliance with the HIPAA Security Rule and HITECH Rules to understand that we don’t quite have this figured out yet.
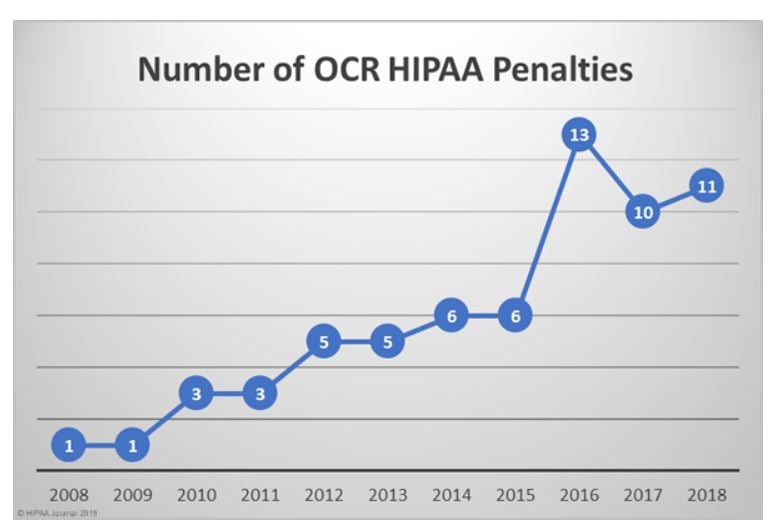
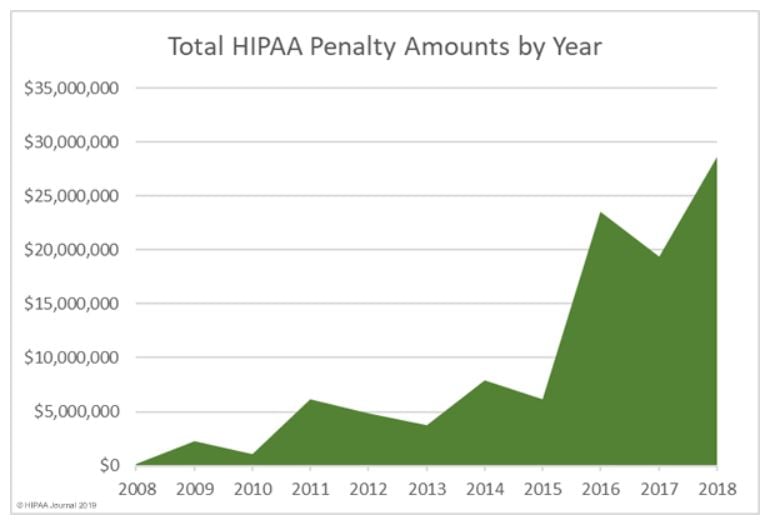
This upward trend could suggest a few things that are happening in the healthcare industry:
- Patient data is increasingly at risk of becoming accessed.
- Cybercriminals are realizing that healthcare organizations are not properly protecting themselves or their patients’ data from breach attempts.
- Cybercriminals are realizing the monetary value of patient data.
- Additional efforts need to be taken for internal security protocol when handling patient data.
- Some IT and information security leaders may be missing vital steps in implementing information security controls.
That’s where guidelines such as the one Adam Kehler wrote are so helpful.
Keeping in mind there is always a risk of being breached, there are also an increasing number of ways to protect data from being accessed and violated by cybercriminals. The guide outlines how to use prescriptive standards such as the Center for Internet Security’s (CIS) Top 20 Critical Security Controls to help address the standards of the HIPAA Security Rule.
I invite you to access a full copy of the ‘Health Center Security & Compliance System Implementation Guide’ today, and see if you are helping to protect your organization’s patient data, as effectively as possible.
For more resources on info-security for healthcare organizations, visit our Health Resource Centre here.
If you have any questions about healthcare info-security, don’t hesitate to reach out to Adam today. The longer companies take to address potential security gaps, the more risk increases for breaches to occur.
Contact Adam below!

.png)

Submit a Comment